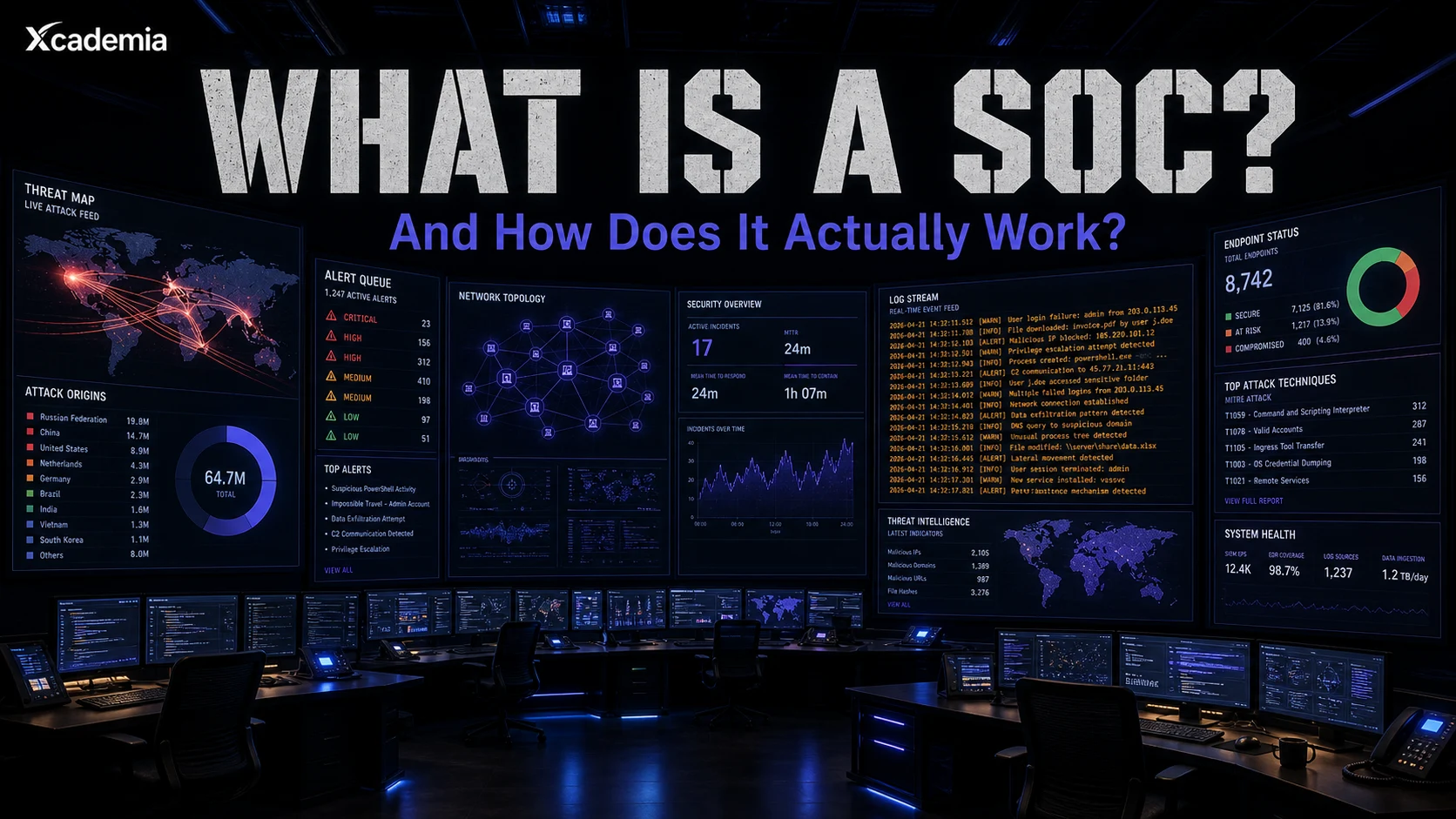
What Is a SOC and How Does It Actually Work?
A Security Operations Centre isn’t a room of screens. It is the function that detects, investigates, and responds to cyber threats in real time. Learn how a SOC actually works, its structure, and why it is critical to modern defence.
The question behind a thousand job applications and a hundred board presentations. Answered properly.
On 7 May 2017, the WannaCry ransomware hit the UK National Health Service. Within hours, hospitals across England were turning patients away. CT scanners were offline. Surgery was cancelled. Staff were writing patient notes on paper.
The NHS had a cyber team. What it did not have was a functioning Security Operations Centre with the capability to detect the threat before it detonated. The difference between a brief disruption and a five-day national crisis was, in large part, the absence of a SOC that could see what was coming.
That is what a SOC is for. This is how one works.
A SOC is not a room full of monitors. It is an operational capability. The room is just where the people sit. The capability is what determines whether your organisation survives the next attack or spends the following week on the front page of the BBC.
The Definition That Does Not Waste Your Time
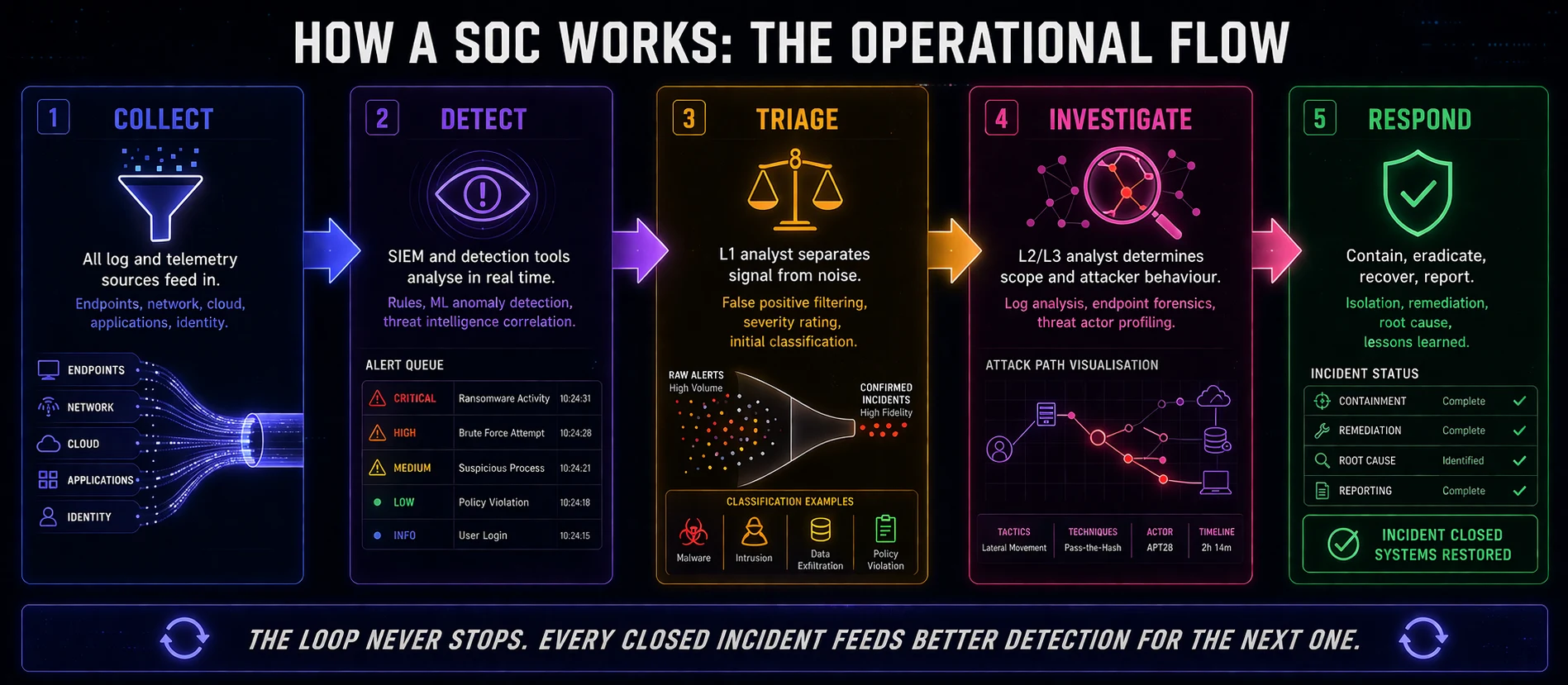
A Security Operations Centre is the function within an organisation responsible for the continuous monitoring, detection, analysis, and response to cybersecurity threats.
Three words do the real work in that definition.
(A) Continuous
Threats do not work business hours. WannaCry hit on a Friday afternoon. NotPetya was deployed at the start of a working week. The 2020 SolarWinds compromise ran undetected for nine months across Christmas, New Year, and every holiday period in between. A SOC that operates only during office hours is not a SOC. It is a gap in your defences with a name.
(B) Detection
Most organisations can respond to an incident once they know about it. The capability failure is almost always detection. The average time between a threat actor gaining access to a network and being discovered is measured in days, sometimes weeks. In the SolarWinds operation, it was months. Detection is the hard problem. Response, by comparison, is the easy one.
(C) Response
Detection without response is just watching. A mature SOC does not alert and escalate. It contains, investigates, eradicates, and recovers. The speed and quality of that response is what separates an incident that costs an afternoon from one that costs a quarter.
The SOC is the only function in your organisation that is actively looking for evidence that you have already been breached. Not waiting for an alarm. Hunting.
The Three Tiers: Who Does What
Every SOC is organised around a tiered analyst structure. Understanding the tiers is the starting point for understanding how to build a career inside one, or how to evaluate the maturity of one you are responsible for.
TIER | WHAT THEY DO | QUALIFICATIONS | SALARY RANGE |
|---|---|---|---|
L1 - Triage Analyst | Monitors alerts. Filters false positives. Escalates confirmed incidents. First responder. | Security+, basic SIEM. 0-2 years. | £28K-£38K UK | AED 10K-15K UAE |
L2 - Incident Analyst | Investigates escalated incidents. Threat hunting. Malware triage. Containment. | CySA+, XSOC. 2-4 years. | £40K-£55K UK | AED 16K-24K UAE |
L3 - Senior Analyst / Threat Hunter | Proactive threat hunting. Adversary emulation. Playbook development. Mentors L1/L2. | CISSP, XCISO path. 5+ years. | £55K-£80K UK | AED 25K-40K UAE |
SOC Manager | Runs the team. Reporting to CISO. Budget. Vendor management. SLA accountability. | CISM, XCISM path. 7+ years. | £70K-£110K UK | AED 35K-55K UAE |
The tier structure exists for a practical reason. Not every alert deserves the same level of attention. L1 analysts filter the volume. L2 analysts handle the substance. L3 analysts hunt for what the automated systems cannot see. The manager makes sure the whole operation runs and reports upward.
A mature SOC runs this structure around the clock. Follow-the-sun models distribute shifts across global time zones. 24/7 cover is not optional if you are defending an organisation that operates continuously.
The most common SOC failure is not technical. It is tier collapse. When L1 analysts spend their time on work that should be automated, L2 analysts get overwhelmed, L3 analysts never get time to hunt, and the threats that matter slip through.
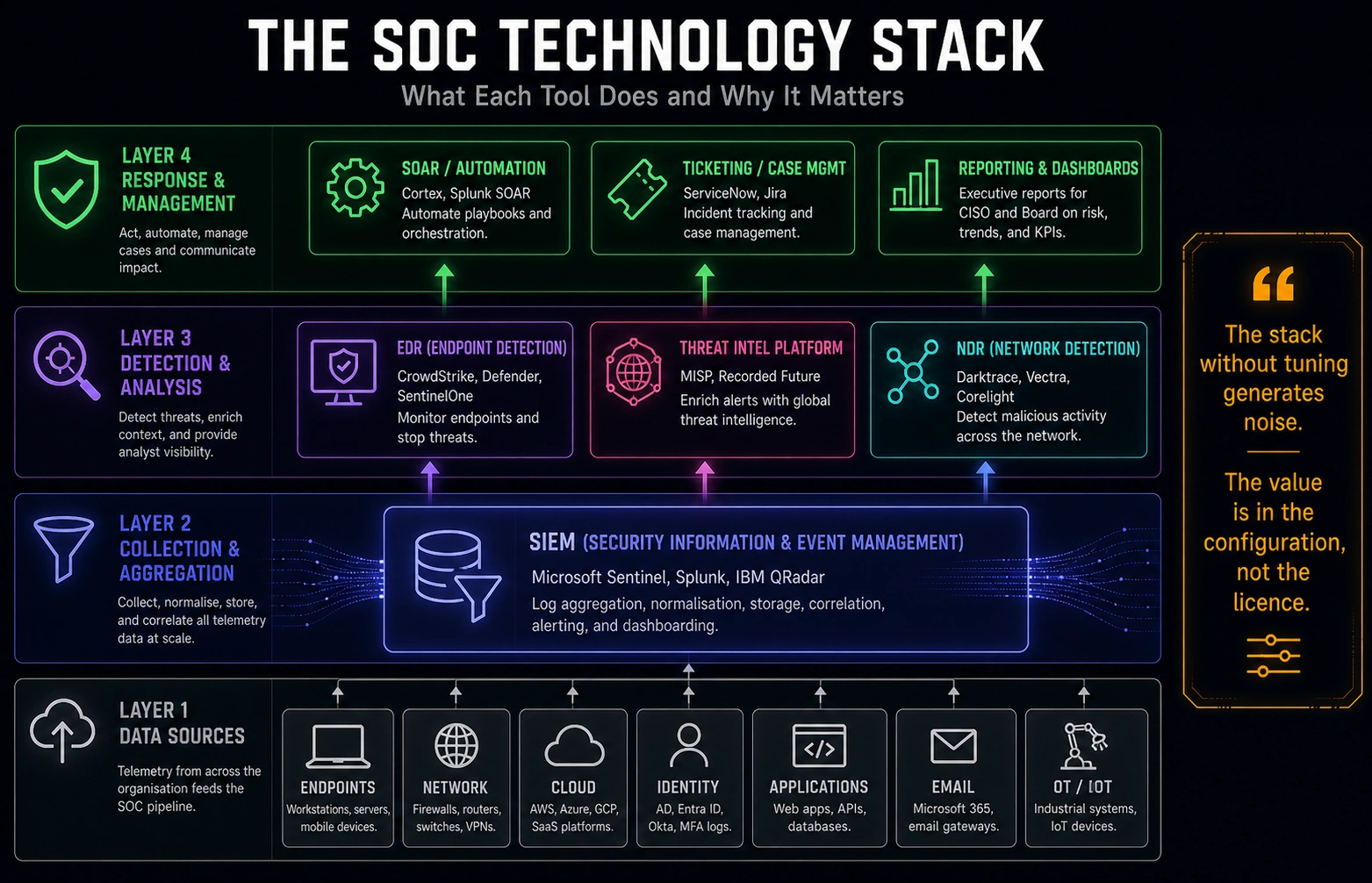
The Technology Stack
A SOC without the right tools is just a team of analysts watching logs scroll by. The technology stack is what gives the team leverage.
SIEM (Security Information and Event Management)
The SIEM is the central nervous system. It aggregates log data from every source in the environment, applies correlation rules, and surfaces alerts. Microsoft Sentinel, Splunk, and IBM QRadar are the dominant platforms in enterprise environments. The SIEM generates the queue that L1 analysts work through. Its quality determines the signal-to-noise ratio the entire team operates against.
EDR (Endpoint Detection and Response)
Where the SIEM watches the network, EDR watches the endpoints. CrowdStrike Falcon, Microsoft Defender for Endpoint, and SentinelOne are the leading platforms. EDR captures process execution, file activity, registry changes, and network connections at the endpoint level. When a threat actor lands on a machine, EDR is often the first tool to see it.
SOAR (Security Orchestration, Automation and Response)
SOAR platforms automate the repetitive tasks that would otherwise consume L1 analyst time. Phishing email triage, IP enrichment, ticket creation, initial containment actions. Palo Alto Cortex XSOAR and Splunk SOAR are the common choices. A well-configured SOAR can handle a significant proportion of low-complexity alerts without human intervention, freeing the team for work that actually requires judgement.
Threat Intelligence Platform
Threat intelligence feeds the detection capability with context. Knowing that an IP address is associated with a known threat actor, or that a file hash matches a piece of malware used in recent campaigns, transforms a raw alert into an actionable finding. MISP, Recorded Future, and built-in intelligence within platforms like CrowdStrike are common implementations.
The tools are only as good as the tuning. A SIEM with out-of-the-box rules generates thousands of alerts per day, most of them noise. The real skill is reducing false positive rates to a level where analysts can focus on the alerts that matter.
Internal vs Managed SOC: The Real Decision
Every organisation that decides it needs a SOC faces the same question: build it or buy it.
Building an internal SOC
An internal SOC gives you control, contextual knowledge, and the ability to build institutional memory about your specific environment. The analysts who work in your SOC learn your network, your users, your normal behaviour. That knowledge is genuinely valuable for detection quality.
The cost is substantial. Fully staffed 24/7 SOC operations require a minimum of 10-12 analysts when you account for shift coverage, holidays, and training. Add tooling costs, management overhead, and the ongoing challenge of retaining skilled analysts in a market where they have many options, and internal SOC becomes a significant investment.
Managed SOC (MSSPs)
Managed Security Service Providers deliver SOC capability as a service. You pay a monthly fee, they monitor your environment and respond to incidents. The cost is lower than building internally. The responsiveness can be faster in the early stages before an internal team is mature. The limitation is context: an MSSP analyst does not know your environment the way an internal analyst does.
The hybrid model
Most mature organisations land somewhere in between. An internal security team handles strategic detection, threat intelligence, and incident command. An MSSP provides 24/7 L1 monitoring and out-of-hours escalation. The internal team focuses on hunting and strategic work. The MSSP handles volume.
The right answer depends on your risk profile, your budget, and what you are actually trying to protect. There is no universal correct answer. There is only the answer that matches your threat model.
What the SOC Career Path Actually Looks Like
The SOC is one of the most reliable entry points into a cybersecurity career, and one of the most demanding environments to progress through. Understanding the path before you commit to it saves considerable time and frustration.
The L1 to L2 transition is the first major gate. L1 roles are accessible with a foundational certification and basic IT knowledge. The transition to L2 requires demonstrated investigation capability, SIEM proficiency, and the ability to work incidents through from detection to containment without constant guidance.
The L2 to L3 transition is harder. L3 analysts are proactive hunters. They write detection rules. They analyse adversary techniques against the MITRE ATT&CK framework. They build playbooks. They mentor. Moving into this tier requires time in L2 and a deliberate investment in developing offensive awareness: understanding how attackers think and move is the foundation of effective threat hunting.
The SOC manager path requires a different set of skills altogether. Technical depth matters, but the role is primarily about people, process, and reporting upward. SOC managers who struggle are usually the ones who are excellent analysts but have not developed the stakeholder management and communication capability the role requires.
The analysts who progress fastest in SOC environments are the ones who treat every alert as a learning opportunity, not a task to close. The difference between a good L1 and a future L3 is usually curiosity, not just competence.
The SOC in 2026: What Has Changed
The SOC of 2026 is not the SOC of 2019. Several shifts have fundamentally altered how effective operations centres work.
AI and automated detection
Machine learning-based anomaly detection has significantly improved signal quality in mature SOC environments. Rather than relying purely on signature-based rules, modern SIEMs and EDR platforms use behavioural baselines to identify activity that deviates from normal even when it does not match a known pattern. The practical effect is catching the threats that signature-based rules miss, at the cost of needing skilled analysts who can evaluate ML-generated alerts critically.
Cloud telemetry
The shift to cloud infrastructure has expanded the attack surface SOCs must monitor. Identity attacks, misconfigured storage, and lateral movement through cloud management planes are now standard parts of the threat landscape. SOCs that were built for on-premise monitoring have had to expand their capability and their tooling significantly.
The analyst shortage
The demand for qualified SOC analysts globally continues to outpace supply. This has two practical effects: experienced analysts command significant salary premiums, and many SOCs are running with fewer people than their workload demands. SOAR automation has partially compensated for headcount gaps, but the gap between the alerts being generated and the human capacity to work them thoughtfully remains significant in many organisations.
The SOC of 2026 runs on three things: good tooling, well-trained analysts, and a detection strategy that prioritises signal quality over alert volume. The organisations that get all three right are significantly more resilient than the ones that optimise for any one of them alone.
The Bottom Line
A SOC is not a compliance checkbox. It is an operational capability that determines whether your organisation can see, understand, and respond to threats before they cause serious damage.
The WannaCry lesson from 2017 has been repeated in various forms every year since. The organisations that weather major cyber incidents are the ones with mature detection and response capability. The ones that do not are the ones that find out about a breach from a journalist, a regulator, or a customer.
Building that capability, whether internally, through a managed service, or in a hybrid model, is one of the highest-value investments any organisation in any sector can make in 2026.
The SOC does not prevent every attack. Nothing does. What it does is change the question from "Were we breached?" to "How quickly did we find it, and how much damage did we limit?"
Ready to go deeper?
Professional Training
Hands-on, mentor-led training aligned with industry certifications.
About the Author
Sharper every day
Daily tutorials, analysis, and career playbooks across all 12 Xcademia disciplines, straight to your inbox. No spam.