What Does a CISO Actually Do on Day One?
Day one reveals the truth no job description does. An inside look at what a CISO actually faces in the first 90 days, from assessing real risk to building a programme that the board will back.
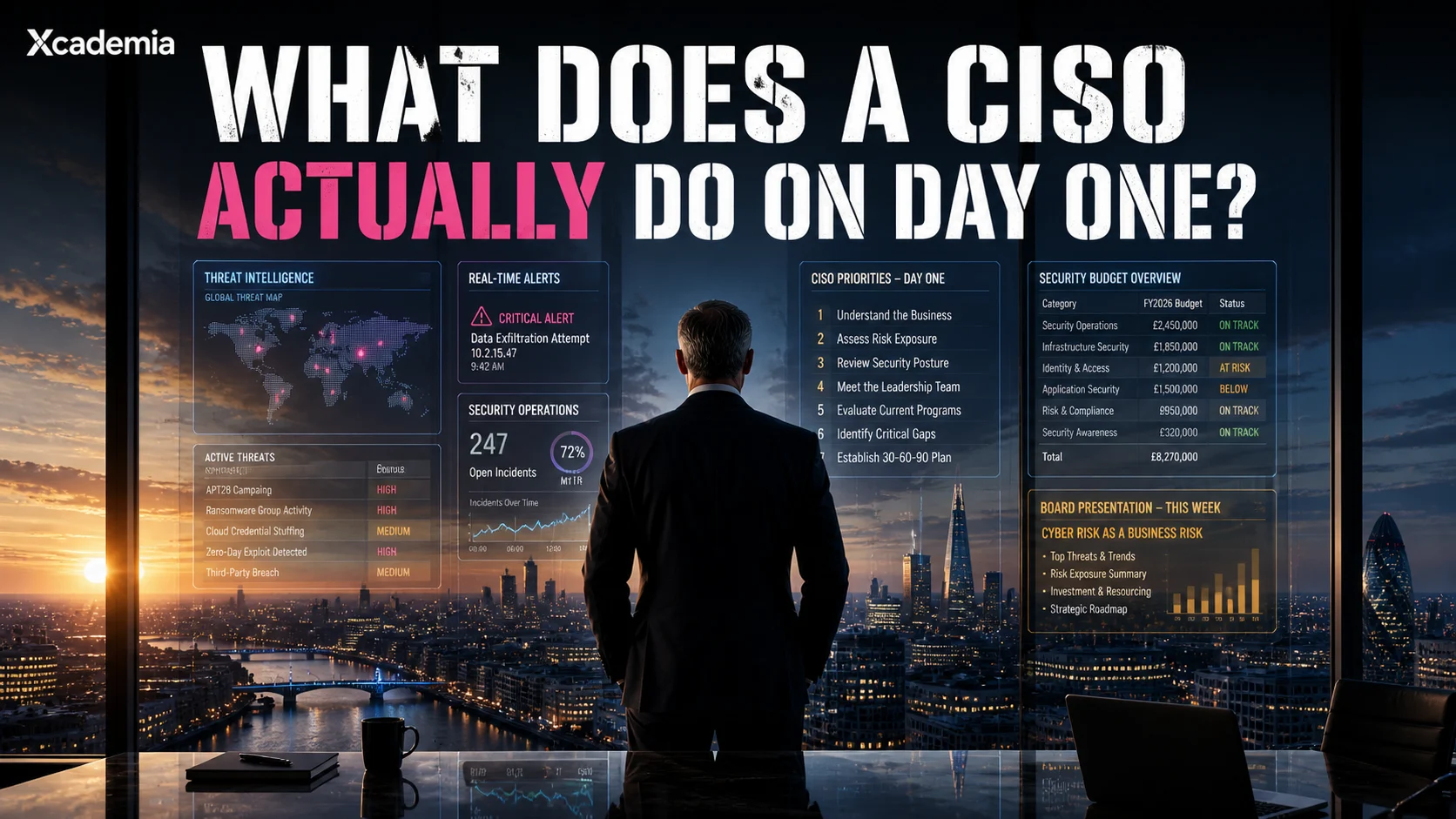
What Does a CISO Actually Do on Day One?
The reality behind the title, the board pack, and the first 90 days that define everything.
Most job descriptions for a CISO run to two pages. They list responsibilities across governance, risk management, compliance, incident response, architecture, vendor management, board reporting, and team leadership. They describe a person with deep technical expertise, strong executive presence, financial acumen, and the communication skills of a diplomat.
What they do not describe is day one.
Day one is different from the role the job description describes. It is noisier, more uncertain, and more revealing of what the organisation actually believes about security than anything written on paper. How a CISO navigates day one, and the ninety days that follow, determines whether they will be effective in the role or whether they will spend two years fighting battles that were lost before they arrived.
The job description tells you what the organisation wants from a CISO. Day one tells you what the organisation has actually built. These are rarely the same thing.
Before Day One: What a Prepared CISO Already Knows
The most effective CISOs do not arrive on day one with a blank page. They have spent the weeks before joining building a picture of the environment they are walking into.
The public threat landscape
What sector is this organisation in? Who are the threat actors targeting that sector? What are the recent significant incidents affecting comparable organisations? A CISO joining a financial institution in 2026 should arrive with a working knowledge of DORA compliance requirements, recent fraud and ransomware campaigns targeting banks, and the specific regulatory expectations of the FCA or relevant authority. That knowledge is available before you set foot in the building.
The organisation's public security posture
A significant amount of an organisation's security posture is visible from the outside before you have access to any internal system. Certificate management. Email security headers (SPF, DKIM, DMARC). Web application security headers. Exposed services and ports. Open-source intelligence about the organisation's infrastructure. A prepared CISO has run this analysis before day one. The results shape the first questions they ask.
The regulatory context
What compliance obligations does this organisation carry? GDPR, NIS2, DORA, ISO 27001, PCI-DSS, SOC 2, HIPAA, sector-specific frameworks? Every obligation has a deadline, a current status, and a consequence for non-compliance. Understanding the regulatory calendar before day one means the CISO can immediately prioritise based on what is most urgent, not just what is most visible.
A CISO who arrives on day one having done this preparation walks into the building already holding the first conversation, not waiting to find out what questions to ask.
Day One: The Reality
Day one is primarily about listening, not acting. The CISO who arrives with a transformation agenda on day one is the CISO who will make enemies before they make progress.
08:00 Induction and access | IT provisioning, system access, building access, introductions. Even at CISO level, day one involves administrative reality. The systems that need to be accessed may not be ready. The access that was promised may require approval chains that nobody has completed. This is useful information: it reveals how the organisation handles privileged access provisioning, and whether the CISO's role is genuinely understood at an operational level. |
|---|
09:30 First conversation: direct team | The security team exists in one of three states when a new CISO arrives: relieved (the previous CISO was a problem), anxious (they do not know what is coming), or sceptical (they have seen CISOs come and go without meaningful change). The CISO's job in the first conversation is to listen, not to present. What are they worried about? What do they feel they lack? What have they been trying to get done that has been blocked? This conversation is where the real programme starts. |
|---|
11:00 First conversation: IT leadership | The relationship between the CISO and the CIO or IT Director is one of the most consequential relationships in the organisation. It can be collaborative and high-functioning, or it can be territorial and adversarial. Day one is about establishing tone. The CISO's job here is to be a peer, not a policeman. To signal that security and technology are aligned, not competing. |
|---|
14:00 First review: existing documentation | What security policies exist? When were they last reviewed? What risk register does the organisation maintain? What incidents have occurred in the past twelve months and how were they handled? What compliance assessments have been conducted and what were the findings? This documentation review is the equivalent of a doctor reviewing a patient's medical history before asking a single question. It shapes every subsequent conversation. |
|---|
16:00 First observation: what is not being said | By the end of day one, the CISO has formed a working hypothesis about the real state of security in the organisation. Not from what people said, but from what they avoided saying. Which topics generated discomfort? Who changed the subject? Whose body language shifted when a particular risk was mentioned? The gaps in the conversation are as informative as the content. |
|---|
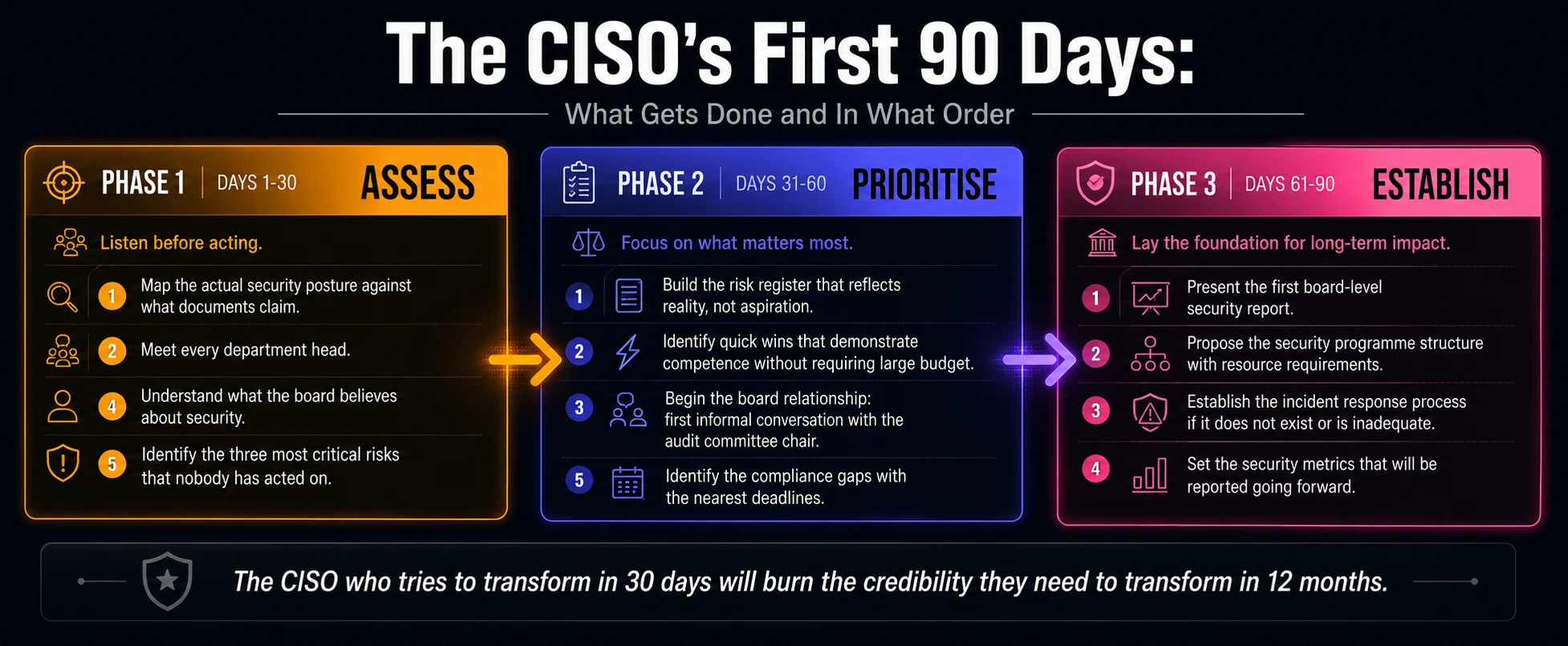
What the CISO Is Accountable For: The Real List
The CISO's accountability spans further than most people outside the role appreciate, and in a different direction than most people inside the organisation expect.
Board and executive accountability
The CISO is accountable for translating technical risk into business language that the board can make decisions on. Not the language of vulnerabilities and CVE scores. The language of financial impact, operational disruption, regulatory consequence, and reputational damage. A CISO who cannot present security risk in business terms will not be heard, regardless of how technically correct their analysis is.
This means understanding how the organisation makes decisions, what the board's risk appetite is, and how security risk compares to the other risks the board is managing. It means learning the language of finance, operations, and strategy, not expecting the board to learn the language of security.
Programme accountability
The CISO owns the security programme: the strategy, the architecture, the policies, the standards, the controls, and the evidence that the controls are working. This is not the same as owning every security decision. The CISO sets the framework within which others make security decisions. The quality of the framework determines the quality of the decisions made within it.
Incident command
When a significant incident occurs, the CISO is the senior decision-maker in the response. Not the most technically skilled person in the room, necessarily, but the person who makes the calls that matter: when to invoke business continuity, when to notify regulators, when to bring in external support, when to brief the CEO. Incident command is a specific skill that requires practice. The CISO who has never run a tabletop exercise is the one who finds out on a live incident how unprepared their team is.
Regulatory accountability
In most regulated sectors, the CISO is the named individual accountable for specific regulatory obligations. Under DORA, GDPR, NIS2, and sector-specific frameworks, the consequence of non-compliance can include personal liability for named officers. This is not a theoretical risk. It is a real accountability that shapes how effective CISOs approach compliance: as a genuine risk management discipline, not a box-ticking exercise.
The CISO role is fundamentally a risk management role. Every technical decision, every budget request, every policy, every board conversation is ultimately about making the organisation's risk profile visible and manageable. CISOs who lose sight of that become excellent technologists in the wrong job.
What Differentiates Effective CISOs From Unsuccessful Ones
Having advised and worked alongside security leaders across multiple sectors, the patterns are consistent.
The ones who succeed
Speak the language of the business before they speak the language of security
Build relationships before they request resources
Pick the three most important things and do them completely, rather than starting ten and finishing none
Present risk in financial terms, not technical terms
Are honest about what they do not know and build the capability to find out
Treat every department head as an ally, not an obstacle
Prepare for incidents before they happen and learn from them when they do
The ones who do not
Arrive with a transformation plan that ignores the organisation's culture and capacity
Make security the enemy of productivity rather than the enabler of it
Spend political capital on battles that do not matter and have none left for the ones that do
Present to the board in technical language that produces confusion, not decisions
Build a security programme that looks complete on paper and provides no real protection
The most common reason a CISO fails is not a lack of technical knowledge. It is a failure to understand that the CISO role is a leadership role first, a risk management role second, and a technical role third.
What Day One Looks Like Six Months Later
The CISO who navigated day one well is, six months in, operating differently from the one who did not.
They have a security programme that the board understands and has approved resources for. They have a direct team that trusts their direction and is working toward shared goals. They have a compliance calendar that is managed rather than reactive. They have an incident response capability that has been tested and is genuinely ready.
They have also made enemies, because effective security always does. The procurement team is unhappy about the vendor risk requirements. The development team is unhappy about the security gates in the pipeline. The board is unhappy about the budget request. An effective CISO accepts this unhappiness as evidence that the programme is real rather than performative.
The CISO who has made no enemies at six months has achieved nothing. Real security changes how organisations operate. That change creates friction. The friction is evidence of progress.
Ready to go deeper?
Professional Training
Hands-on, mentor-led training aligned with industry certifications.
About the Author
Sharper every day
Daily tutorials, analysis, and career playbooks across all 12 Xcademia disciplines, straight to your inbox. No spam.