The 10 Most Devastating Cyber Attacks in History
A definitive analysis of the 10 most devastating cyber attacks in history, covering what happened, the scale of damage, and the lessons that continue to shape modern cybersecurity.
What happened. What it cost. What it changed forever.
History is written by the survivors. In cyber warfare, the survivors are the ones who learned from what happened, and changed their defences before the next attack arrived.
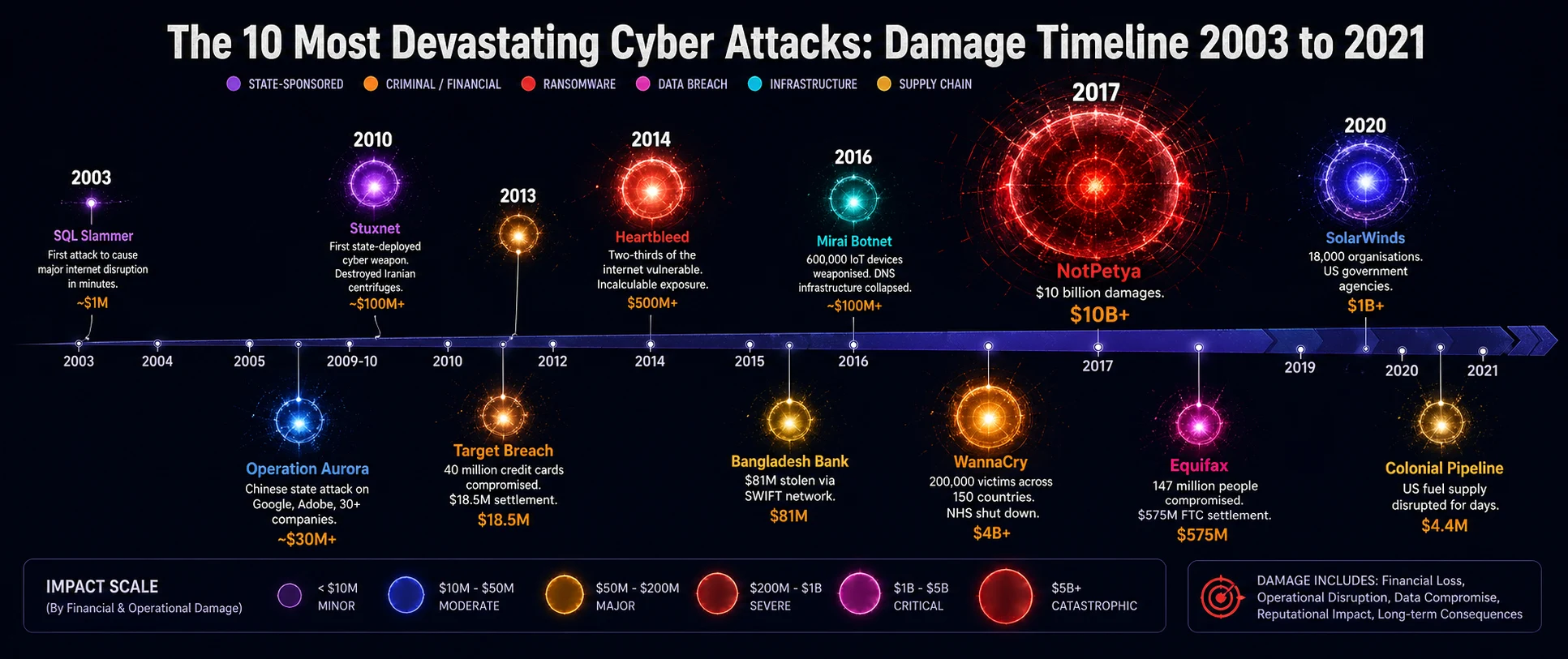
The ten incidents in this article are not ranked by technical sophistication. They are ranked by consequence: the scale of damage, the permanence of what changed, and the lessons that every security professional carries forward from each one.
Some of these attacks destroyed infrastructure. Some destroyed organisations. Some destroyed trust in the systems that billions of people depend on. All of them changed how the world thinks about digital security.
Every attack on this list was preventable. Not by magic, not by unlimited budget, but by the application of principles that were known at the time and not followed. That fact is more unsettling than the attacks themselves.
The Ten Attacks
2009 to 2010 Operation Aurora | ||
|---|---|---|
| ||
In late 2009, attackers believed to be working for Chinese intelligence began a sustained intrusion campaign targeting the source code repositories of Google, Adobe, Juniper Networks, Rackspace, and more than two dozen other major technology companies. The campaign used a previously unknown vulnerability in Internet Explorer to gain initial access, then moved laterally with extraordinary patience through corporate networks. Google discovered the intrusion when the attackers attempted to access Gmail accounts belonging to Chinese human rights activists. The company went public — an almost unprecedented decision at the time. The IP stolen from these operations informed a decade of Chinese technology development. The real damage was never quantifiable. WHAT IT CHANGED: It established that nation-states were conducting systematic corporate espionage through cyber means at scale, and that no technology company was too large or too sophisticated to be a target. Supply chain and zero-day vulnerability management became boardroom topics. |
2016 Mirai Botnet | ||
|---|---|---|
| ||
Mirai was elegant in its brutality. It scanned the internet for IoT devices — cameras, routers, DVRs — that still used their factory default credentials. It found them in the hundreds of thousands. It recruited them silently into a botnet. Then it turned that botnet against Dyn, a DNS provider whose infrastructure underpinned Twitter, Reddit, Netflix, Spotify, CNN, and dozens of other major services. On 21 October 2016, those services went dark for millions of users across the US and Europe. Mirai demonstrated that the billions of poorly secured connected devices we had embedded in our infrastructure were not just insecure individually. They were a collective weapon. WHAT IT CHANGED: IoT security became a regulatory and engineering priority almost overnight. It exposed the catastrophic risk of default credentials and the absence of any security baseline in consumer connected devices. The vulnerabilities Mirai exploited still exist in millions of devices today. |
2016 Bangladesh Bank Heist | ||
|---|---|---|
| ||
On the night of 4 February 2016, attackers who had spent months inside the Bangladesh Bank's network submitted 35 fraudulent transfer requests through the SWIFT interbank messaging system, attempting to move $951 million from the bank's account at the Federal Reserve Bank of New York. Five transfers totalling $101 million succeeded before the fraud was detected. Of that, $81 million reached accounts in the Philippines and disappeared into the casino industry, recovering only a fraction. A printer running out of paper and a bank clerk's suspicion about unusual spelling in a transfer request stopped the remaining $850 million. The attack demonstrated that SWIFT, the backbone of international financial transfers, could be weaponised from the inside. WHAT IT CHANGED: It permanently changed how financial institutions approach privileged access to interbank messaging systems. SWIFT introduced a mandatory security controls framework. The incident made clear that the financial infrastructure connecting global banking had been treated as trusted by design when it should have been verified at every step. |
2017 Equifax Data Breach | ||
|---|---|---|
| ||
In May 2017, attackers exploited a known vulnerability in Apache Struts, a web framework used in Equifax's online dispute portal. The vulnerability had been publicly disclosed and a patch had been available for two months. Equifax had not applied it. Over 76 days, the attackers moved through 48 distinct databases, exfiltrating names, Social Security numbers, birth dates, addresses, and credit card numbers for nearly half the adult population of the United States. The breach was discovered in July 2017. The patch that would have prevented it had been available since March. The company's CEO, CTO, and CSO all resigned. The FTC settlement of $575 million was the largest ever imposed for a data breach at the time. WHAT IT CHANGED: It demonstrated that the most sophisticated attack vector in the world can be a 76-day unpatched vulnerability in a public-facing system. Patch management was elevated from an IT operational concern to a board-level governance priority in organisations across every sector. |
May 2017 WannaCry | ||
|---|---|---|
| ||
On 12 May 2017, a piece of ransomware began spreading across the internet with a capability that nobody had seen at that scale before: it moved laterally across networks without any human interaction, exploiting a Windows vulnerability called EternalBlue that had been developed by the NSA and stolen by a group called the Shadow Brokers. Within hours, it had hit the UK's National Health Service, locking clinical staff out of systems, forcing the diversion of ambulances, and cancelling thousands of patient appointments. It hit Telefonica, FedEx, Deutsche Bahn, and Renault. It spread to 150 countries in a single day. A 22-year-old security researcher discovered a kill switch embedded in the malware's code — a domain that, when registered, caused the malware to stop spreading. That accident of discovery prevented substantially greater damage. Microsoft had released a patch for EternalBlue two months earlier. The NHS had not applied it. WHAT IT CHANGED: WannaCry changed healthcare cybersecurity policy in the UK permanently. It established ransomware as a civilisational risk, not a corporate inconvenience. It made the case, which no security professional had been able to make convincingly before, that unpatched systems in critical infrastructure are a matter of national security. |
April 2014 Heartbleed | ||
|---|---|---|
| ||
Heartbleed was not an attack in the conventional sense. It was a vulnerability in OpenSSL, the cryptographic library used to secure HTTPS connections across an estimated 66% of the internet. A single missing bounds check in code allowed an attacker to read 64 kilobytes of memory at a time from affected servers, potentially exposing private keys, login credentials, and session tokens. The vulnerability had existed in OpenSSL since December 2011. It was discovered and disclosed in April 2014. In the window between its introduction and its disclosure, any sufficiently motivated actor could have been exploiting it silently. The Canadian Revenue Agency confirmed that 900 Social Insurance Numbers were extracted using Heartbleed in the days after disclosure. The full extent of exploitation before disclosure was never established and never will be. WHAT IT CHANGED: It shattered the assumption that open-source code is inherently more secure because more people review it. It exposed the critical infrastructure dependency on a small volunteer-maintained project. The OpenSSL Foundation's annual budget at the time of disclosure was $2,000. The internet ran on it. |
June 2017 NotPetya | ||
|---|---|---|
| ||
NotPetya was designed to destroy. It was disguised as ransomware but there was no recovery mechanism because the encryption was irreversible by design. It was delivered initially through M.E.Doc, Ukrainian accounting software required by law for any company doing business in Ukraine. From that entry point, it spread globally within hours using EternalBlue and a credential-harvesting tool called Mimikatz. Maersk, the shipping conglomerate responsible for 20% of global container trade, lost every one of its 45,000 PCs and 4,000 servers. Its operations were restored only because a single domain controller in Ghana happened to be offline during the attack and preserved the Active Directory needed for recovery. Merck lost months of pharmaceutical production. FedEx's TNT subsidiary lost $400 million and never fully recovered its systems. The entire operation was aimed at Ukraine. The rest of the world was collateral damage. |
2009 to 2010 Stuxnet | ||
|---|---|---|
| ||
Stuxnet was the first time in history that a nation-state deployed a cyber weapon to cause physical destruction to another nation's infrastructure. It targeted the Siemens programmable logic controllers managing the centrifuges at Iran's Natanz uranium enrichment facility. It caused the centrifuges to spin at speeds that physically destroyed them, whilst simultaneously reporting normal operation to the monitoring systems that engineers were watching. The operators watched their equipment fail and had no idea why. Stuxnet is estimated to have destroyed approximately one fifth of Iran's nuclear centrifuges and set the programme back by years. Its discovery and analysis by security researchers fundamentally changed how the world understood what cyber weapons were capable of. The code was extraordinarily sophisticated. It used four previously unknown zero-day vulnerabilities, an almost unheard-of level of offensive investment. WHAT IT CHANGED: Stuxnet changed everything. It established that cyber attacks could cause physical destruction. It demonstrated that critical industrial control systems were legitimate military targets. It opened Pandora's box: every nation with offensive cyber capability began asking how they could build something similar, and every defender began asking how they would protect against it. |
December 2020 SolarWinds (Sunburst) | ||
|---|---|---|
| ||
SolarWinds was not the most destructive attack on this list in terms of immediate financial damage. It was the most strategically significant in terms of what it achieved. Attackers inserted malicious code into a software update for SolarWinds Orion, a widely used IT management platform. The update was signed with a legitimate SolarWinds certificate and distributed to 18,000 customers as a routine patch. It included a backdoor that lay dormant for two weeks after installation to avoid detection, then began establishing command-and-control communications that mimicked legitimate Orion traffic. US government agencies including the Treasury, State Department, and Department of Homeland Security were compromised for months before the intrusion was discovered, not by the government's own monitoring, but by a private security firm that noticed a suspicious device on its network. The full scope of what was accessed remains classified. WHAT IT CHANGED: SolarWinds destroyed the assumption that software updates from trusted vendors are trustworthy by definition. It elevated software supply chain security to a national security priority across every government that understood what had happened. It demonstrated that the most sophisticated attackers do not break down the front door. They walk in through the back, dressed as a routine update. |
2017 The WannaCry and NotPetya Year | ||
|---|---|---|
| ||
No single attack takes the top position in this list. Instead: 2017 as a year. In the space of six weeks, two nation-state operations using the same stolen NSA exploit demonstrated that the world had crossed a threshold it had not acknowledged crossing. WannaCry brought down NHS hospitals and showed that patient care could be held hostage by ransomware. NotPetya showed that a weapon aimed at one country could cause $10 billion in collateral damage to global commerce without the attacker intending any of it. The same exploit. Two different actors. Two different objectives. One catastrophic conclusion: the interconnectedness of global digital infrastructure meant that cyber weapons could no longer be contained to their intended targets. They would go wherever the network went, and the network went everywhere. WHAT IT CHANGED: 2017 forced a generational reassessment. Governments that had been treating cyber security as a technical matter began treating it as a question of national survival. Organisations that had been deferring security investment began understanding that the deferral had a cost, and that the invoice could arrive without warning, in the middle of a working day, with no recovery option. |
What Every Attack Has in Common
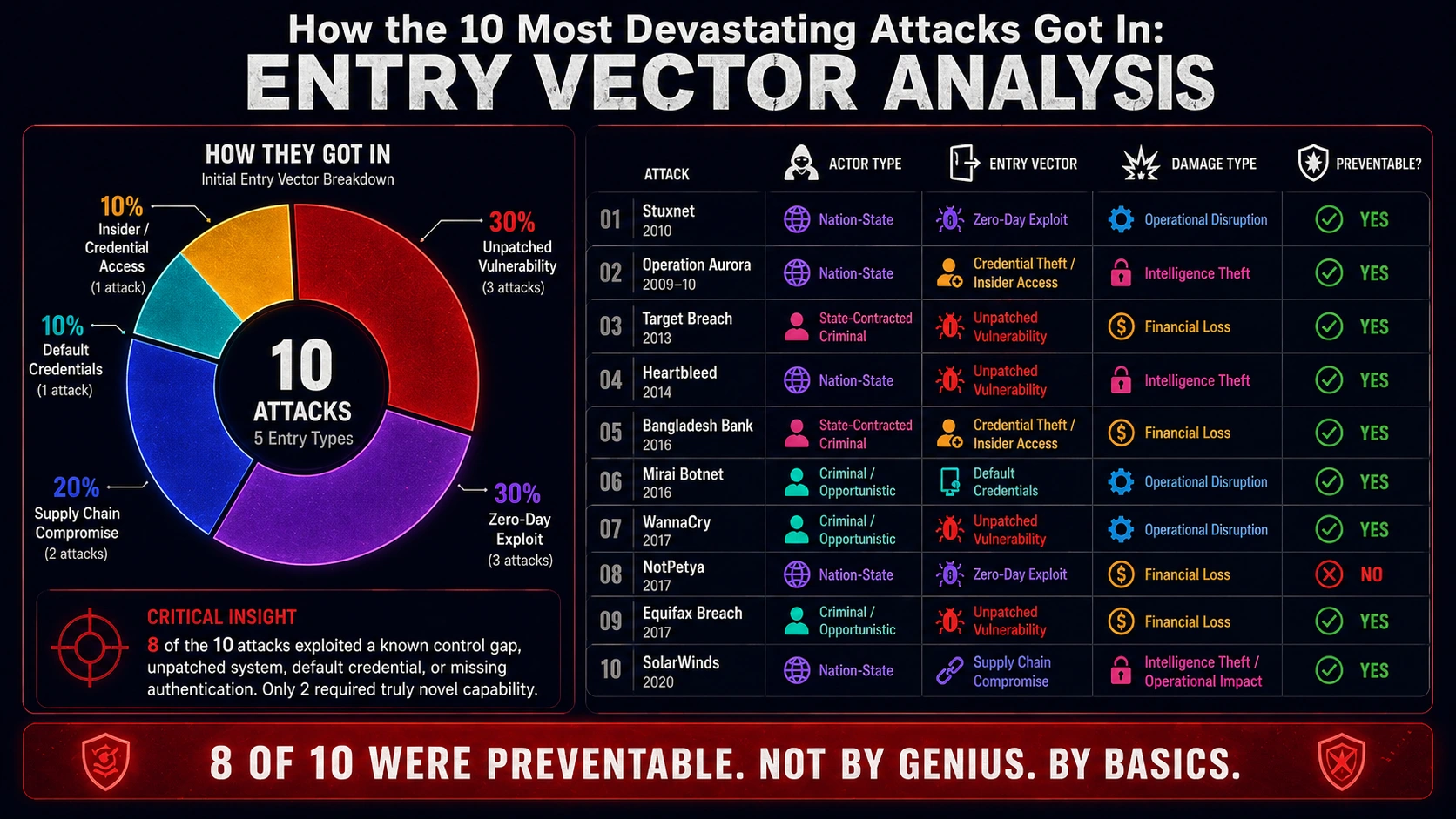
Read these ten incidents carefully and a pattern emerges that is more uncomfortable than any individual attack.
Eight of the ten exploited something that was known, addressable, and not addressed. An unpatched vulnerability. A default password. A trusted update that was not verified. A privileged account that was not monitored. Not exotic, classified, nation-state-only capabilities. Basics that every organisation in the world knows it should have in place and does not always implement.
Two of the ten used genuinely novel capabilities: Stuxnet's four simultaneous zero-days, SolarWinds's supply chain insertion. Even those depended on the target's failure to monitor, segment, or detect.
The most sophisticated cyber weapons in history did not succeed because they were unstoppable. They succeeded because the fundamentals were missing. That is not a comfortable fact. It is an actionable one.
The five lessons every security professional carries from this list
Lesson 1: Patch management is national security. Three of the ten most devastating attacks in history exploited known vulnerabilities for which patches existed and had not been applied. The window between patch release and patch application is the window attackers live in.
Lesson 2: Supply chain is your attack surface. You are as vulnerable as the least secure software you install. SolarWinds and NotPetya both demonstrated that trusted software can be the weapon. Vendor risk management is not an audit checkbox. It is a primary defence.
Lesson 3: Detection is as important as prevention. In SolarWinds, attackers were present for up to 14 months before discovery. In Operation Aurora, the intrusion ran for months. The assumption that prevention is sufficient has cost organisations and governments billions. Detection capability, behavioural monitoring, and threat hunting are not advanced topics. They are fundamentals.
Lesson 4: Recovery planning is non-negotiable. Maersk rebuilt its entire global IT infrastructure in ten days during NotPetya because it found one functioning domain controller and executed a prepared recovery plan at extraordinary speed. Most organisations could not have done what Maersk did. Most organisations have not tested their recovery capability under realistic conditions.
Lesson 5: The attack aimed at someone else will reach you. NotPetya was aimed at Ukraine. It reached Maersk in Denmark, Merck in the US, and FedEx globally within hours. The assumption that targeted attacks will stay targeted is not an assumption that the evidence supports.

The World After These Attacks
The ten incidents in this article did not happen in isolation. They happened because the world had built a digital infrastructure of extraordinary interconnectedness without building the defensive capability to match it. They happened because organisations treated security as a cost rather than a survival function. They happened because governments treated cyber as a technical domain rather than a strategic one.
The world that exists today is the product of what these attacks forced. GDPR was accelerated by the scale of data breaches. NHS Cyber was built after WannaCry. The US Cybersecurity and Infrastructure Security Agency was elevated in response to SolarWinds. National cyber strategies across the UK, EU, US, and UAE were written with these incidents as the evidence base.
The attacks are over. The lessons are permanent. And the next wave of attacks, augmented by AI, operating at machine speed, targeted with precision that the attackers on this list could not have imagined, is already building.
History does not repeat itself. But the professionals who have not learned it will live it again. The organisations that studied these ten incidents and acted on the lessons are in a different position from the ones that read the headlines and moved on.
Ready to go deeper?
Professional Training
Hands-on, mentor-led training aligned with industry certifications.
About the Author
Sharper every day
Daily tutorials, analysis, and career playbooks across all 12 Xcademia disciplines, straight to your inbox. No spam.