How to Break Into Cybersecurity in 2026
A practical guide to breaking into cybersecurity in 2026 without a computer science degree or technical experience. Discover which path fits your background, the certifications and skills that matter, how to gain experience, and what employers actually look for in entry-level candidates.
How to Break Into Cybersecurity in 2026
With no prior experience, no computer science degree, and no idea where to start.
The most common question Xcademia receives from professionals outside the technology sector is some version of the same thing: I want to work in cybersecurity. I do not have a computer science degree. I do not have technical experience. Is it too late, and where do I start?
The honest answer to the first question is no. It is not too late. The cybersecurity talent gap is structural and persistent. Organisations across every sector are looking for qualified professionals, and they cannot find enough of them. That gap does not discriminate based on how you spent your twenties.
The honest answer to the second question is more complex. Where you start depends on what you are bringing with you, what kind of cybersecurity work you want to do, and how much time and investment you can make. This guide gives you the actual map, not the motivational version.
The people who successfully transition into cybersecurity are not always the most technically gifted. They are the ones who understood the landscape before they started, chose the right entry point for their background, and built their capability systematically rather than randomly.
The Myth You Need to Dispense With First
Cybersecurity is not one job. It is a collection of disciplines that have almost nothing in common except that they all involve protecting digital systems and the information within them.
A penetration tester and a GRC analyst both work in cybersecurity. One spends their days trying to break into systems using technical exploitation techniques. The other spends their days reviewing policy frameworks, managing audit programmes, and ensuring the organisation meets its regulatory obligations. Their skill sets overlap at the margins. Their day-to-day work could not be more different.
The career transition question is not "how do I get into cybersecurity?" It is "which part of cybersecurity suits my background, my strengths, and what I actually want to spend my time doing?"
Most career transition advice treats cybersecurity as a single destination. It is not. It is a continent. Knowing which country you are heading to changes everything about how you get there.
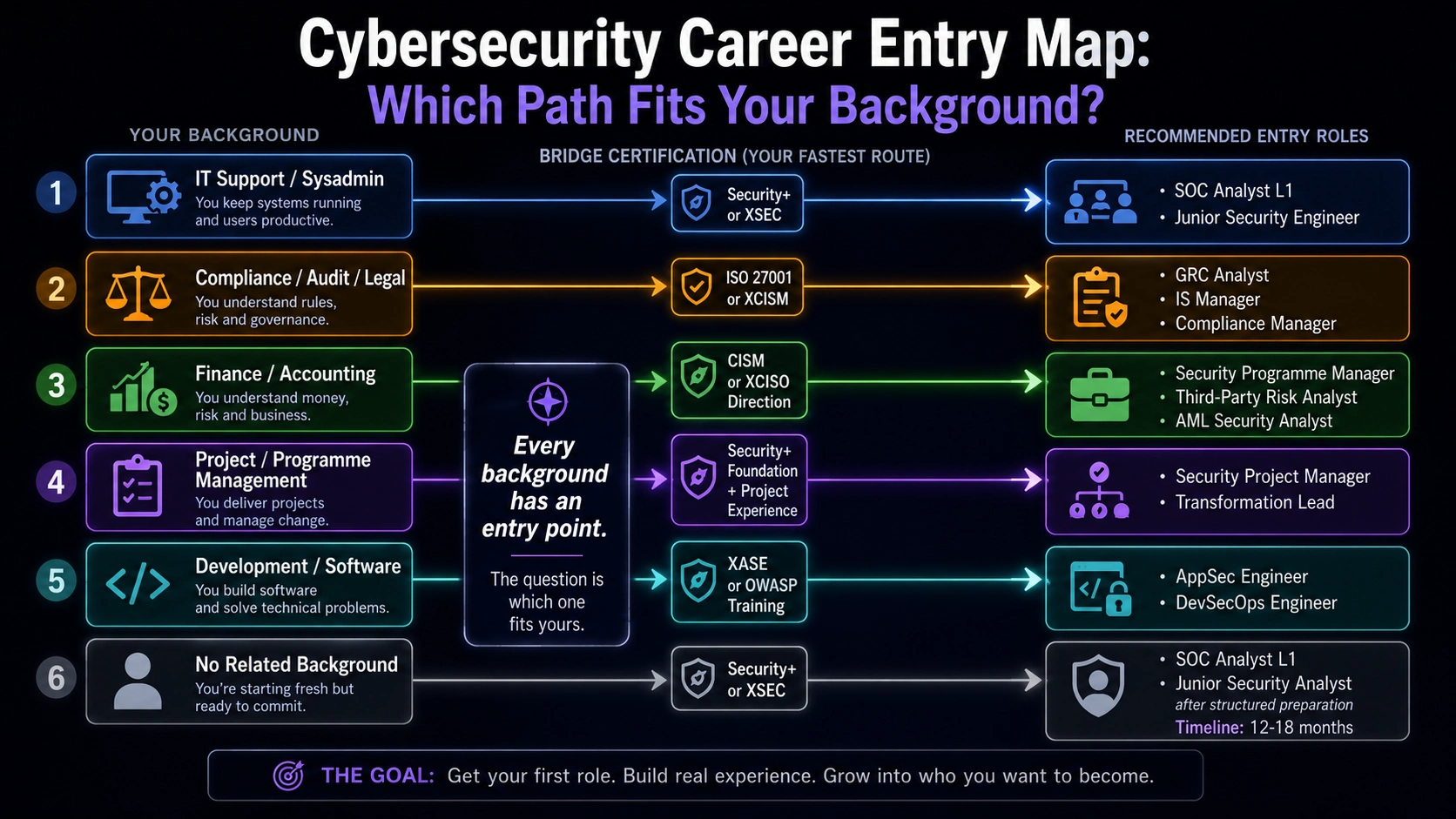
Which Cybersecurity Path Matches Your Background
Your prior experience is not irrelevant. It is the raw material for a faster transition than you probably think is possible.
If you come from IT support or systems administration
This is the most natural technical transition. You already understand networks, operating systems, user management, and troubleshooting. The step into a SOC analyst role or a security engineer role is shorter than from a non-technical background. Your first certification should be Security+ or XSEC to formalise the security knowledge layer on top of your IT foundation. Target SOC L1 roles or junior security engineer positions as your first cybersecurity role.
If you come from a compliance, legal, or audit background
GRC is your entry point and it is a well-paid one. Governance, risk, and compliance roles require the skills you have already developed: reading frameworks, writing policies, managing audit processes, communicating risk to non-technical stakeholders. The certifications that formalise this path include ISO 27001 Lead Implementer, CISM, and for the practitioner track, XCISM or XCRISC. These roles pay well, are in high demand, and do not require deep technical knowledge to enter.
If you come from finance or accounting
Security programme management, CISO advisory, and third-party risk management all benefit heavily from financial literacy. The CISO role itself requires someone who can build and defend a security budget, calculate risk in financial terms, and speak to the board about investment returns on security spending. AML and financial crime roles in cybersecurity-adjacent functions are also a direct application of your existing skills.
If you come from project or programme management
Security programme delivery, transformation programmes, and large-scale compliance implementation projects all need people who can manage timelines, stakeholders, dependencies, and budgets. The technical security knowledge can be learned. The project discipline is already yours. Target security project manager and security programme lead roles as your entry point.
If you are starting from no related background
It is harder but far from impossible. The path is longer and requires more deliberate investment. The entry point is typically a foundation certification (Security+ or XSEC), followed by a home lab for practical experience, followed by a junior SOC or helpdesk-with-security-focus role. Budget twelve to eighteen months of deliberate preparation before your first cybersecurity job application.
The career transition that works is the one that builds on what you already know. The transition that fails is the one that treats your previous experience as irrelevant and tries to start from zero in a technical specialism that takes years to develop.
The Practical Pathway: Step by Step
This is the sequence that works. Not the fastest possible sequence. The one that produces a sustainable career rather than a qualification without a job.
1 | Get your foundation certification right Months 1-3 Security+ for maximum market recognition. XSEC for applied capability evidence alongside or instead. Do not skip this. Do not try to jump straight to CEH or CISSP. The foundation certification exists because it works: it confirms baseline knowledge to employers and it identifies your own gaps. |
|---|
2 | Build a home lab Months 1-4 (concurrent with step 1) A home lab is the difference between knowing about security and having done it. TryHackMe, Hack The Box, and Blue Team Labs Online provide structured environments for practising offensive and defensive skills without needing expensive hardware. Set aside two to three hours per week minimum. Document everything you do. Your home lab notes are your first portfolio. |
|---|
3 | Get a job adjacent to cybersecurity Months 3-9 Your first job does not have to be a cybersecurity job. An IT support role at a company with a security team gets you inside the building. A helpdesk role where you handle security tickets gives you real exposure. A compliance assistant role gives you regulatory experience. The adjacent role gives you income, experience, and access to the people who will give you your first referral. |
|---|
4 | Apply for your first cybersecurity role Months 9-18 SOC Analyst L1 is the most accessible entry point for career changers with a foundation certification and some practical experience. Junior security analyst roles at MSSPs are another strong entry point: the breadth of client environments provides faster learning than most in-house roles. Apply to more roles than you think is necessary. The conversion rate for early-career cybersecurity applications is low. Volume matters. |
|---|
5 | Specialise deliberately Year 2 onwards Once you have twelve months of real cybersecurity experience, you have enough context to know which specialism you want to pursue. That is when the specialisation investment makes sense: XSOC for SOC career depth, XASE for AppSec direction, XCTI for threat intelligence, XCIR for incident response. Specialise based on what you have learned about what you are good at and what you enjoy, not based on what pays most in someone else's career. |
|---|
What Nobody Tells You About the Application Process
The cybersecurity job market has a frustrating paradox at the entry level: there is a talent shortage globally, and there are also many qualified people who cannot get their first role. The paradox is explained by the gap between "qualified" and "hirable."
The ATS problem
Most applications are filtered by Applicant Tracking Systems before a human reads them. Your CV needs to contain the keywords from the job description to survive this filter. That means tailoring every application, not submitting a generic CV. Security+ should appear as "CompTIA Security+" and also as "Security+" because different job descriptions use different terms. The same applies to every tool and technology you mention.
The experience paradox
Many entry-level job descriptions list two to three years of experience as a requirement. This is not a hard barrier. It is a wish list. Apply anyway. The specification was written by someone who wanted an experienced person at an entry-level salary. The hiring manager will consider a well-prepared candidate without the years if the application demonstrates capability rather than just listing credentials.
What actually gets you the interview
A home lab you can talk about with specific examples of what you built and what you learned
CTF (Capture the Flag) competition participation, with rankings or write-ups you can reference
A GitHub repository with security-related projects or write-ups
A specific cover letter that demonstrates you understand the organisation's sector and threat landscape
A referral from someone inside the organisation or the industry
The candidate who has not completed a CTF competition but has written a detailed blog post about their home lab investigations will get more interviews than the candidate with three certifications and nothing practical to discuss.
The Salary Reality
Entry-level cybersecurity salaries vary significantly by location, employer type, and specialism. These are realistic figures for 2026, not aspirational ones.
UK: SOC Analyst L1 £25,000-£35,000. Junior Security Analyst £28,000-£38,000. GRC Analyst (entry) £30,000-£40,000.
UAE/Dubai: SOC Analyst L1 AED 8,000-14,000/month. Junior Security Analyst AED 10,000-16,000/month. Zero personal income tax.
USA: Entry-level security analyst $55,000-$80,000 depending on location. Government and DoD roles typically higher with clearance premium.
These figures double or more within three to five years of deliberate career development. The cybersecurity salary ceiling is genuinely high. The entry-level figures reflect the cost of not yet having demonstrated capability, not a limit on what the field pays.
Entry-level salaries in cybersecurity are not the story. The trajectory is the story. The SOC analyst on £28,000 today who builds their capability deliberately is the security architect on £80,000 in five years. The investment in getting in pays back significantly.
Ready to go deeper?
Professional Training
Hands-on, mentor-led training aligned with industry certifications.
About the Author
Sharper every day
Daily tutorials, analysis, and career playbooks across all 12 Xcademia disciplines, straight to your inbox. No spam.