What Is Cyber Warfare? The Definitive Guide for 2026
Cyber warfare is transforming global security in 2026, affecting governments, businesses, and individuals. This article explains what cyber warfare is, how it works, key threats, and why cybersecurity skills are essential today.

What Is Cyber Warfare? The Definitive Guide for 2026
In 2010, a centrifuge at an Iranian nuclear facility started destroying itself. No explosion. No airstrike. No troops on the ground. Just a piece of software, later identified as Stuxnet, doing what conventional weapons could not do without triggering a war.
That was not a cyberattack in the way most people understand the term. That was an act of cyber warfare.
The distinction matters. And in 2026, as AI lowers the cost of offensive cyber operations and critical infrastructure becomes more connected than ever, every organisation, not just governments, needs to understand what cyber warfare actually is.
The Definition That Actually Holds Up
Cyber warfare is the use of digital attacks by one state, or a state-sponsored actor, to damage, disrupt, or destroy another state's critical systems, infrastructure, or national security capabilities.
It is distinct from:
Cybercrime: Financially motivated. The attacker wants money and will take it from any available target.
Hacktivism: Ideologically motivated. The attacker wants to make a point. Visibility is the goal.
Cyber espionage: Intelligence motivated. The attacker wants information without being detected.
Cyber warfare is about strategic effect. The attacker wants to degrade the adversary's ability to function, project power, or respond. Sometimes it runs alongside a conventional military operation. Sometimes it runs instead of one. 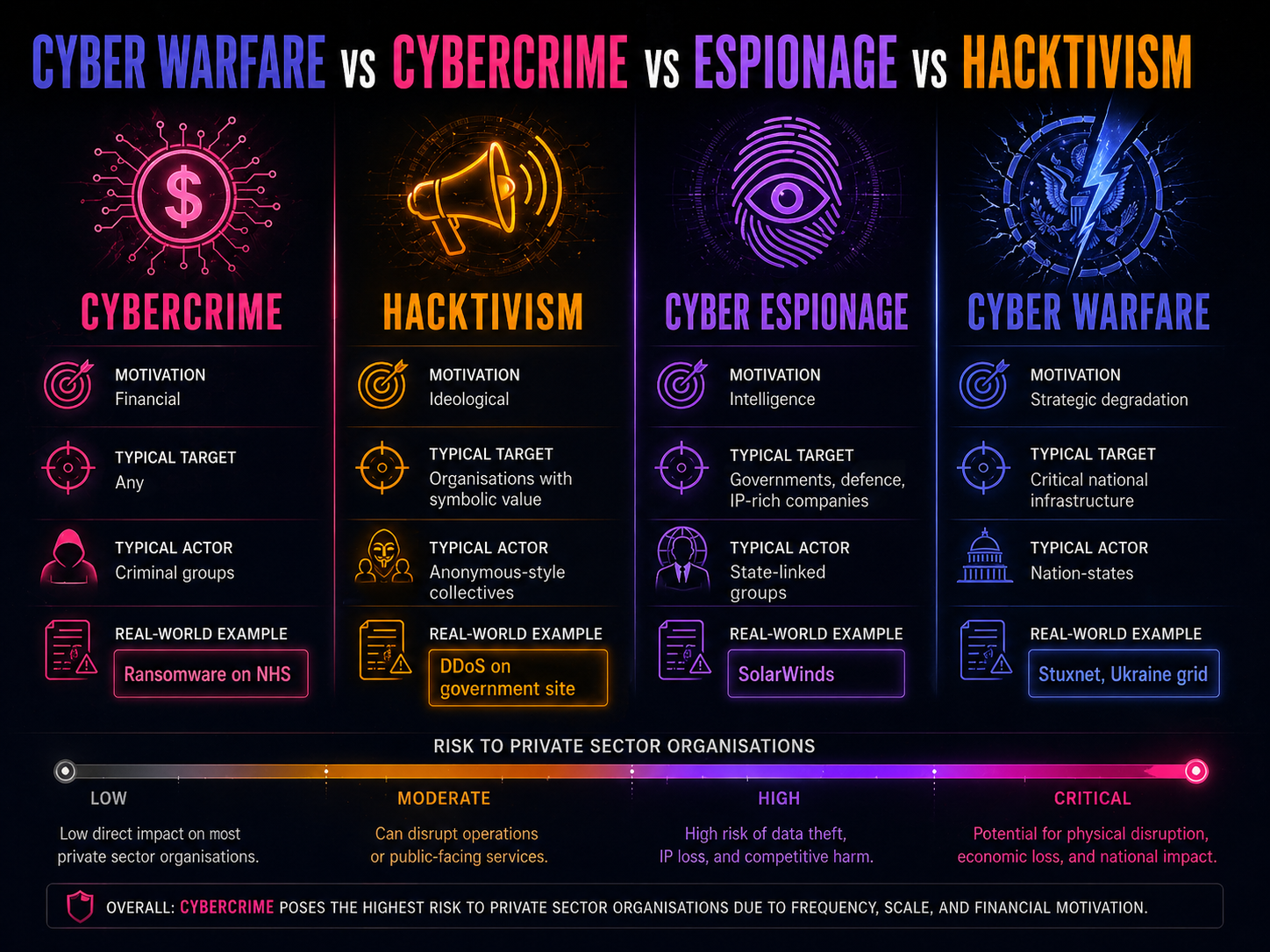
What Cyber Warfare Actually Looks Like
The textbook definitions are clean. The reality is messier and far more instructive.
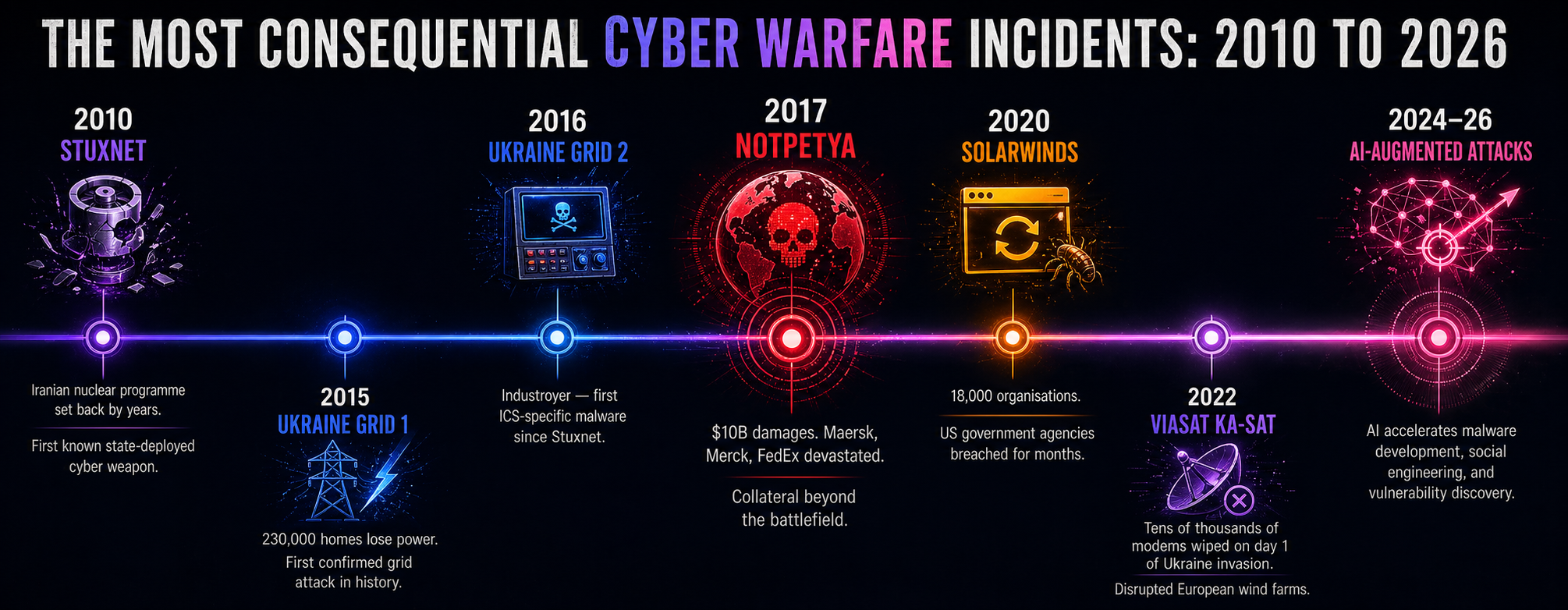
Stuxnet (2010)
Widely attributed to a joint US-Israeli operation, Stuxnet targeted the industrial control systems running Iran's uranium enrichment centrifuges. It caused the machines to tear themselves apart whilst simultaneously reporting normal operation to monitoring systems. It set Iran's nuclear programme back by years. No military strike. No diplomatic incident that could be formally attributed. Just code.
Ukraine Power Grid Attacks (2015 and 2016)
Russian-linked threat actors cut power to hundreds of thousands of Ukrainian homes in two separate attacks. The second attack, using malware known as Industroyer, was the first confirmed malware specifically designed to disrupt industrial control systems at this scale since Stuxnet. It was a test. It was also a warning.
SolarWinds (2020)
Attackers, later attributed to Russian intelligence services, inserted malicious code into a software update for SolarWinds Orion, used by thousands of organisations including US government agencies. The compromise went undetected for months. The operation was not about destroying anything. It was about access, patience, and positioning.
NotPetya (2017)
Deployed initially against Ukrainian systems, NotPetya spread globally within hours, causing an estimated $10 billion in damages. It was disguised as ransomware but was actually a wiper — it destroyed data with no intention of recovery. It crossed borders not by design but by the interconnected nature of global business networks.
Who Are the Threat Actors?
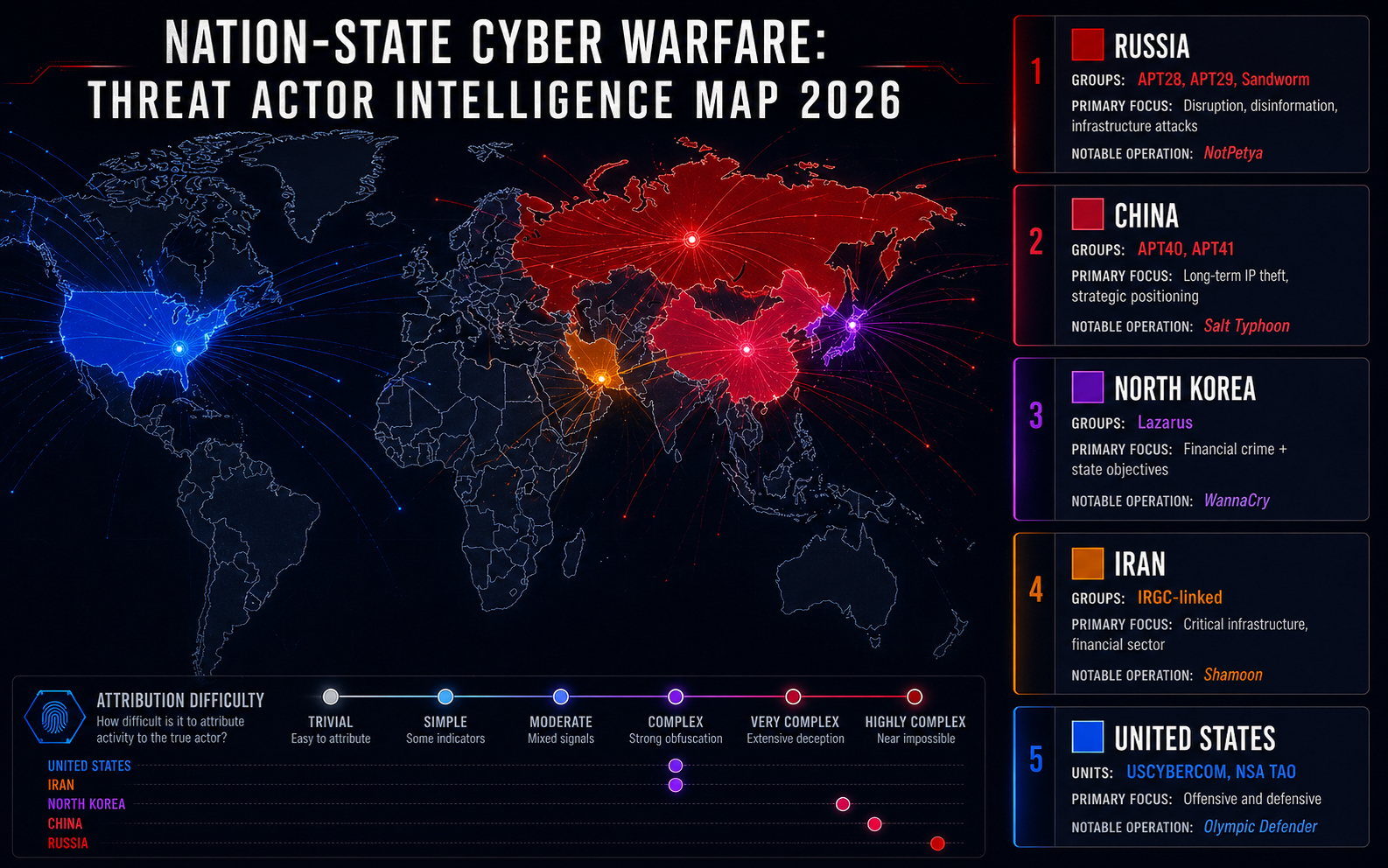
Five nation-states dominate the cyber warfare landscape in 2026.
Russia: Operates through the GRU and FSB. Known groups: Fancy Bear (APT28), Sandworm. Operations blend espionage, disruption, and disinformation.
China: Long-term strategic intelligence collection. APT40 and APT41 target IP, defence contractors, and technology companies. Goal: capability acquisition over decades.
North Korea: Lazarus Group combines state-directed objectives with financial crime, funding the regime through cryptocurrency theft and bank breaches.
Iran: Significantly expanded since Stuxnet. IRGC-linked groups target critical infrastructure in adversary states and financial institutions.
United States: Operates through USCYBERCOM and NSA TAO. Both defends and conducts offensive operations. Confirmed via documents released in 2013.
Beyond these five, proxy groups, criminal organisations contracted by states, and hacktivist collectives operating with tacit state approval complicate attribution significantly.
Why This Matters to Organisations, Not Just Governments
The infrastructure that modern militaries depend on is largely owned and operated by the private sector. Power grids. Telecommunications networks. Financial systems. Logistics and supply chains. Healthcare systems.
NotPetya was not an attack on private companies. It was an attack on Ukraine that spread. The distinction offers no comfort to the shipping company that lost 45,000 PCs and had to rebuild from scratch.
Organisations in these sectors face elevated risk:
Energy and utilities
Financial services and banking
Defence contractors and the defence supply chain
Healthcare and pharmaceuticals
Telecommunications
Transportation and logistics
Government contractors at any tier
The AI Dimension
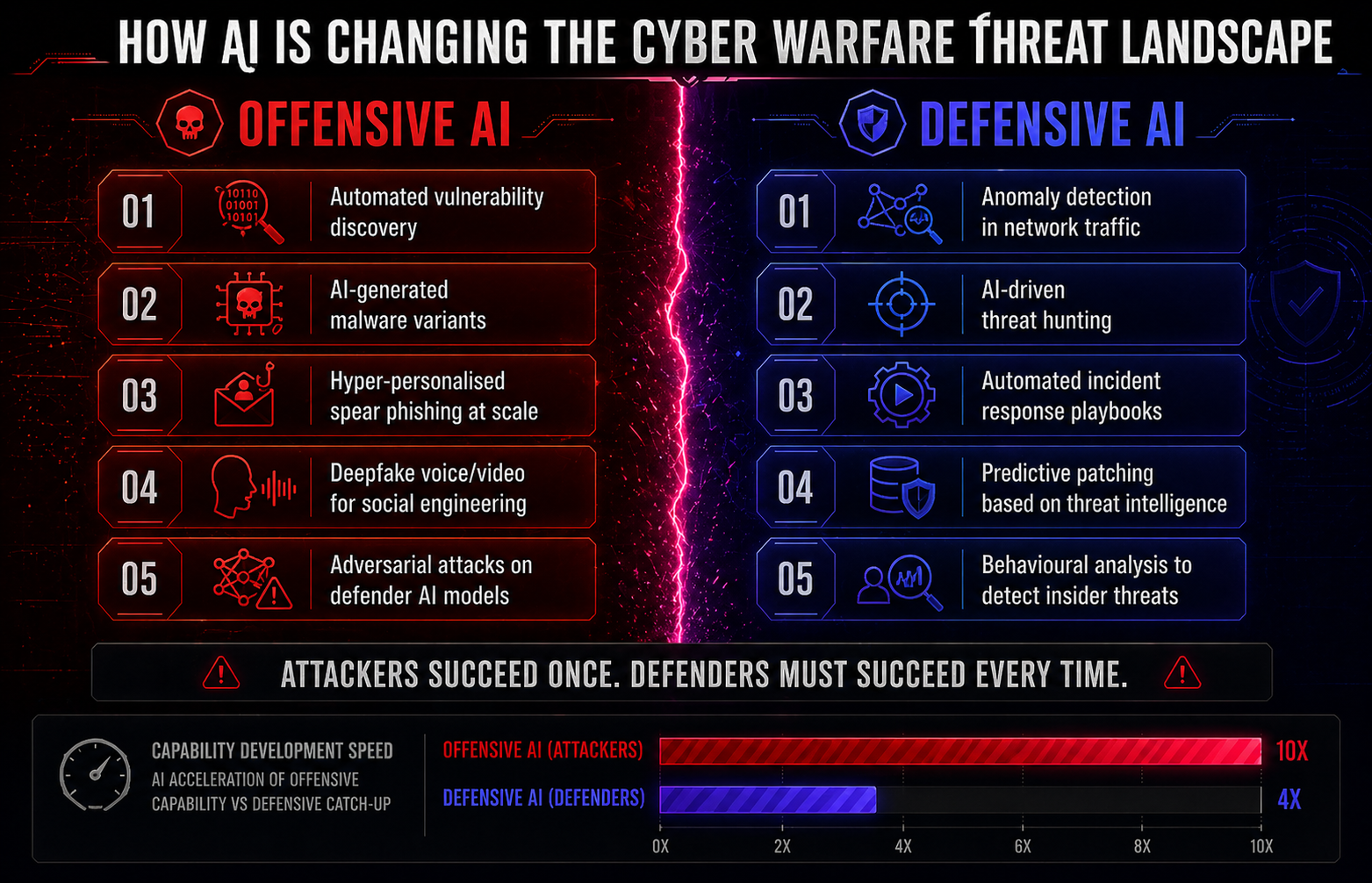
The barriers to conducting sophisticated cyber operations are falling.
AI is accelerating malware development. It is enabling more convincing social engineering at greater scale. It is identifying vulnerabilities faster than defenders can patch them.
Defenders face a structural disadvantage. Attackers only need to succeed once. Defenders need to succeed every time.
What Professionals Need to Know
Understanding cyber warfare at a conceptual level is not sufficient for the professionals responsible for defending organisations against it.
The frameworks that underpin national and organisational cyber defence, including the NCSC Cyber Assessment Framework, ISO 27001, and NIST, were developed with threat landscapes like this in mind. But knowing the framework is not the same as being able to apply it under operational pressure.
The professionals who are effective in this environment have practised detection, response, and recovery in realistic conditions. They understand how threat actors move through a network, how to hunt for indicators of compromise, and how to make rapid decisions when systems are under active attack.
What Comes Next
Cyber warfare will not become less relevant. The geopolitical conditions driving it are not improving. The technology enabling it is becoming cheaper and more accessible. The attack surface is expanding as operational technology, previously air-gapped from the internet, becomes connected.
The question is not whether your organisation will be affected by the broader cyber warfare environment. The question is whether your people are trained to recognise, respond to, and recover from it when it arrives.
Ready to go deeper?
Professional Training
Hands-on, mentor-led training aligned with industry certifications.
About the Author
Get weekly insights
Fresh articles on cybersecurity, AI, and leadership delivered to your inbox.