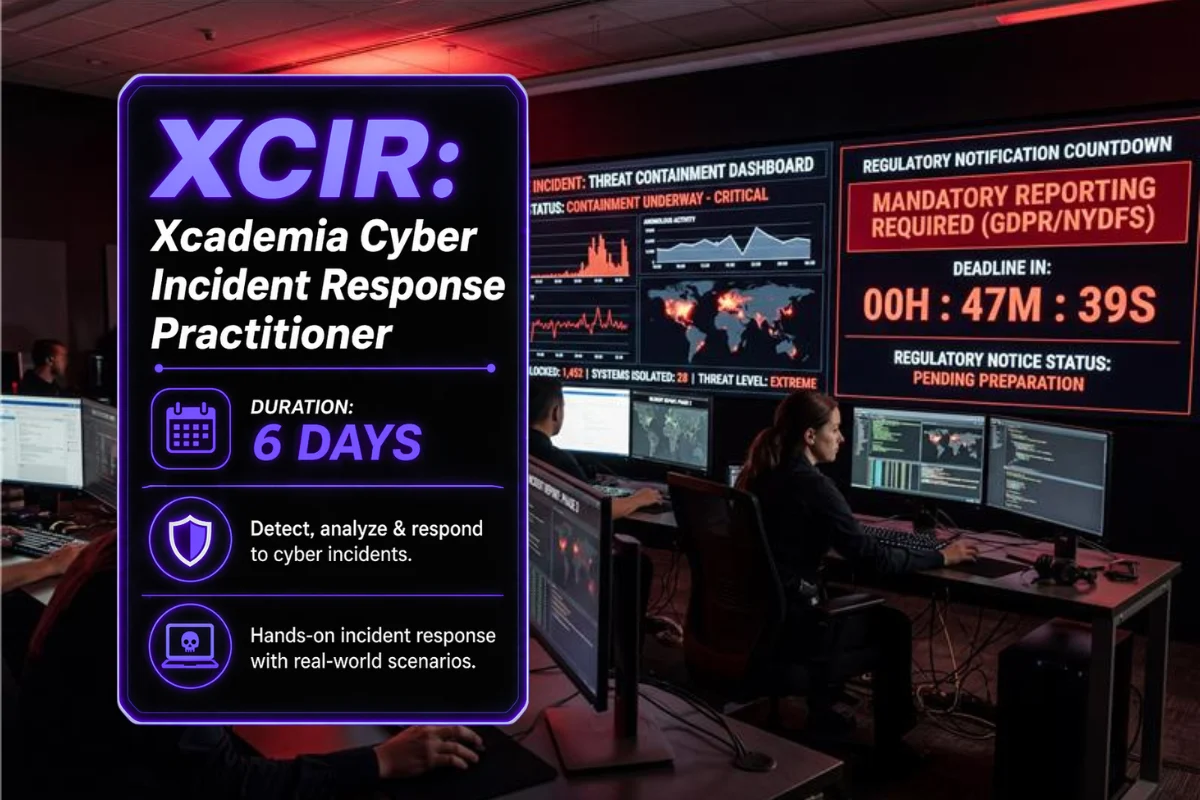
A cyber incident does not wait. When the call comes, the incident responder who has only passed a multiple choice test is dangerous. XCIR is built for professionals who need to perform under pressure: containing the attacker, preserving evidence, communicating with leadership, and meeting the regulatory notification timelines that NIS2 and DORA now mandate.
Across six instructor-led days, participants build capability across the complete IR lifecycle: preparation and planning, detection and scoping, containment strategy, evidence preservation, eradication, recovery, and post-incident activities. Sessions cover Windows and Linux IR, active directory compromise response, cloud IR across AWS and Azure, ransomware playbooks, insider threat response, and regulatory notification workflows aligned to NIS2 Article 23, DORA Article 17, and UK GDPR Article 33.
On Day 6, participants manage a live simulated incident from initial detection through containment, eradication, recovery, and final incident report. The senior practitioner observes decision-making, technical execution, communication, and regulatory compliance throughout. XCIR certificate and Practitioner Assessment Report issued together. Aligned with NIST SP 800-61, ISO 27035, CISA IR Playbooks, NIS2, DORA, UK GDPR, and NHS DSPT.